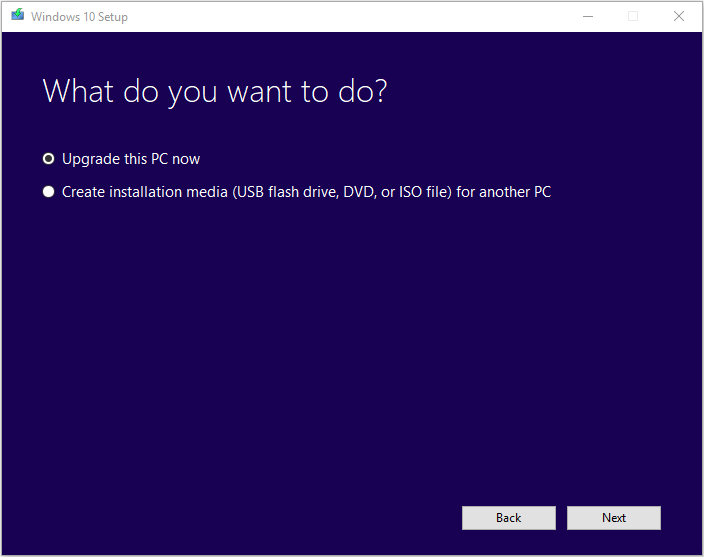
How to get around the 'insufficient memory available' error while updating old apps or installing new ones on Android phones with low internal memory - Quora
please update 7z package (error: not enough memory for bomb detection, 7-Zip cannot find the code that works with archives, Can not open the file as archive) · Issue #11140 · batocera-linux/batocera.linux ·
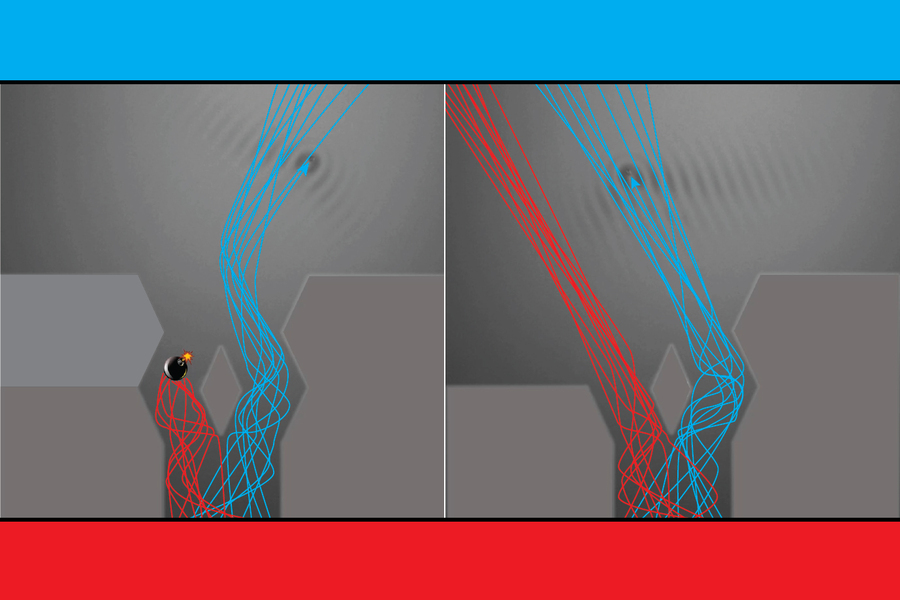
MIT researchers observe a hallmark quantum behavior in bouncing droplets | MIT News | Massachusetts Institute of Technology






![How To Fix there is not enough memory to complete this operation [Solved] - YouTube How To Fix there is not enough memory to complete this operation [Solved] - YouTube](https://i.ytimg.com/vi/WLs10aNYths/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLDimVkyxoIVXgdTM9VrGAGCRhQ3hg)
![How To Fix there is not enough memory to complete this operation [Solved] - YouTube How To Fix there is not enough memory to complete this operation [Solved] - YouTube](https://i.ytimg.com/vi/m0pW9uIV6-8/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLCFLr9IJEQh7nlROiUZUZscJl-LOA)



![[FIXED] Not Enough Memory Resources are Available to Process this Command [FIXED] Not Enough Memory Resources are Available to Process this Command](https://i.ytimg.com/vi/5cP5arlWzZk/maxresdefault.jpg)
![How To Fix there is not enough memory to complete this operation [Solved] - YouTube How To Fix there is not enough memory to complete this operation [Solved] - YouTube](https://i.ytimg.com/vi/rSH45P7pD_0/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLCO6vq2mTF8IKcfCXI4VPB9qup9Eg)





