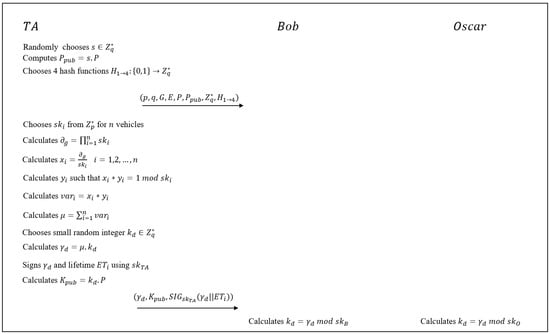
Mathematics | Free Full-Text | Cryptanalysis of an Authentication Scheme Using an Identity Based Generalized Signcryption

Sensors | Free Full-Text | Breaking Trivium Stream Cipher Implemented in ASIC Using Experimental Attacks and DFA
Fujitsu Laboratories, NICT and Kyushu University Achieve World Record Cryptanalysis of Next-Generation Cryptography - Fujitsu Global